… Or why stealing software is stupid (and wrong). A small guide to detect software theft for those who are not reverse engineers.
Under my previous post the user Xylitol reported a web-page (hxyp://martik-scorp.blogspot.com/2010/12/show-me-loaded-drivers.html) by someone called “Martik Panosian” claiming that my driver list utility was his own.
Now, the utility is very small and anybody who can write a bit of code can write a similar one in an hour. Still, stealing is not nice. 🙂
Since I can’t let this ignominious theft go unpunished :P, I’ll try at least to make this post stretch beyond the specific case and show to people who don’t know much about these sort things how they can easily recognize if a software of theirs has been stolen.
In this specific case, the stolen software has been changed in its basic appearance (title, icon, version information). It can easily be explored with a software such as the CFF Explorer. In this case the CFF Explorer also identifies the stolen software as packed with PE Compact. If the CFF Explorer fails to recognize the signature, it’s a good idea to use a more up-to-date identification program like PEiD.
However, packing an application to conceal its code is a very dumb idea. Why? Because packers are not meant to really conceal the code, but to bind themselves to the application. What is usually difficult to recover in a packed application is its entry-point, the IAT and other things. But the great majority of the code is usually recoverable through a simple memory dump.
Just select the running application with an utility such as Task Explorer, right click to display the context menu and click on “Dump PE”.
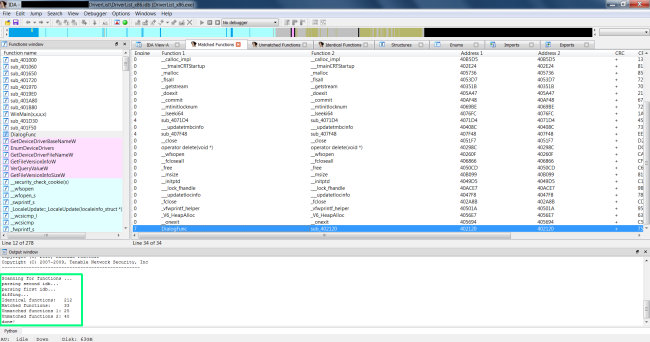
Now the code can be compared. There are many ways to compare the code of two binaries. One of the easiest is to open it with IDA Pro and to use a binary diffing utility such as PatchDiff2. If the reader is doing this for hobby and can’t afford a commercial license of IDA Pro, then the freeware version will do as well.
Just disassemble both files with IDA Pro and save one of the idbs. Then click on “Edit->Plugins->PatchDiff2” and select the saved idb.
Let’s look at a screenshot of the results:
As it is possible to see, not only were the great majority of functions matched, but they also match at the same address, which proves beyond doubt that they are, in fact, the same application.
It’s important to remember that a limited number of matches is normal, because library functions or some basic ones may match among different applications.
A comparison of two applications can even be performed manually with IDA Pro, just by looking at the code, but using a diffing utility is in most cases the easiest solution.

Let Martik Panosian have his say now.. (if he dares)
Over on PortableFreeware.com, one of the alert users (Ruby) discovered Martik rebranding software to portray himself as the author, presumably to draw traffic for his website and money for ads there. He first claimed to have been loaned the code but when I contacted the author, he explained he’d never shared the code with anyone. The whole episode got deleted but you can still find the thread over on Google cache:
http://webcache.googleusercontent.com/search?q=cache:rOhhzPrNUz4J:www.portablefreeware.com/forums/viewtopic.php%3Ff%3D4%26t%3D6939+site:portablefreeware.com+bootsafe&cd=2&hl=en&ct=clnk&gl=us&client=firefox-a
I don’t know if he still does, but he was listing what looked like pirated software on his site, so I don’t really think his conception of what’s ethical in software development is totally clear. I never verified for myself that this was actually the case, but he didn’t bother to really defend himself.
I understand the position behind software piracy: I don’t have the money and I really need X software. However, making money from developers who are kind enough to give away their work for free? Totally unethical.
Webfork: yes, indeed the site of this Martik looks full of rebranded software (including keygens for other programs). Seems to be a habit.
Of course, pirating because of the impossibility to pay is understandable. But claiming intellectual ownership is another thing, as you said. I’ve never complained when people put my software on their web-pages (full of ads) and didn’t even link my web-page or credited me as the author, as long as they didn’t change the executable and claim copyright on the software themselves.
The problem is that those kind of people who do that, change the software, then pack it with a commercial packer and in the process even think they’re very clever.
Hello,
This is Martik. the owner of hxyp://martik-scorp.blogspot.com.
I’m here to tell you guys few things:
First of all I’m not making any money (even 1 penny) from any softwares or keygens. This all just for FUN and as you said hobby!
Second, why some people crack softwares (commercial ones) and spread them (crack/patch/keygens) over Internet. is it legal or what? do they obey copyright or something?
Instead, I rip their keygens and patches and publish them with others name. so whats wrong with that. Cracks has no copyrights, am I right?
I want to, they feel the same as people who they crack others commercial softwares.
Thats all!
(I dunno if you will publish this or not, whatever…)
Of course I publish it. Your reply is ludicrous. On a scale of 1 to 10, where one is represented by a husband telling his wife that he doesn’t know how that long blond hair landed in his underwear, and ten equaling Ted Bundy blaming the porn industry for his crimes, your comment scores a sound 8,5 of absurdity.
First off, you’re not ripping off only keygens and cracks, as this post demonstrates.
Second, those who write keygens and cracks are often young boys or generally people who don’t know the damage they cause to developers and small/medium companies. This doesn’t excuse them, but it offers a perspective. However, you don’t have the moral high ground to “punish” them. Let alone claiming to do so, while even more damaging the software owners by spreading the cracks and keygens.
About your claim of not making 1 penny out of it, it is highly dubious. Your web-page is full of ads and even popularity has a value. I don’t know what fun and hobby it is to rip off the work of others.
I agree totally with Daniel.
Daniel: Please delete the link to his website or modify it in some way to make sure it doesn’t directly link there.
Martik: Since you conveniently misunderstand whatever people tell you, let me be clear: MANY people don’t like what you’re doing. Please delete your website.
http://www.mywot.com/en/scorecard/martik-scorp.blogspot.com
Also: important reading for anyone who doesn’t understand the concept:
http://en.wikipedia.org/wiki/Plagerism
Webfork:
those MANY people are only the crackers. what did you expect?
I can show you that LOT OF people like my page!
The nerve of this guy!
Daniel,
BTW. The latest latest release does not contain the “Signature” folder and PE Detective and Identifier do not work.
Thanks!
Hey Gapend, I can’t confirm. I tried both the multiplatform version and the x86 one. Both seem to work correctly, have the signatures and PE Detective works.
Maybe it’s the fault of a broken download. I don’t know.
Could you try again?
Martik is such a great haxxor (sic).. every 5 years old child can use reshacker to rip a keygen…
He just want to take pride for a job he didnt done….and took money with ads on this website…
Altought it is illegal, and maybe immoral, people are making keygen “for the lulz”..Isnt taking pride for using reshacker the bad thing ins the story?
martik is ripping to gain some sort of money,”fame” so he can claim “yeah, i have the biggest one”..
This is just stupid and totally childish …
Oh and, “if lot of people like your page” . lol.. We cant stop stupid people to be stupid. On My website i kill kitties, a lot of people like it ,so its good 😀
Anyway, thanks for your website, DP
Thanks, Sally!
But you should stop killing kitties 😛
j/k
I wouldn’t get to riled up about this supposed “Martik’s” comments. In case some of you are new to the web, there is another hobby people have called “trolling.” What ii is exactly is hard to define with exactness but these “Martik” comments are more than likely a case of it. Sorry to disappoint anyone who thought they were “talking back” so to speak with the “‘REAL’ bad guy.”
You might want to check this out apparently this guy got his app copied by Martik with no dredit and was able to get the page on Martik’s blog linking to the stolen app removed. Judging from the dialogue in it the original Martik poster on here may have infact been the REAL Martik. Sorry it’s in Spanish so here is the Google translated link: http://translate.google.com/translate?u=http%3A%2F%2Fcrackinglandia.reversingcode.com%2F%3Fp%3D107&sl=&tl=en&safe=off
jsday: from the incorrect use of the English language, I’d say it’s him. Plus, the rationalization of the misdeed goes beyond trolling.
But anyways, it’s not very important.
I agree with Daniel, martik is definitely not the author of the software. He cannot claim about using the same UI either as Daniel’s analysis revealed.
Martik please admit it and stop posting such lame replies.
Ps.
*anyways is incorrect according to the Oxford dictionary 😛
Tom: damn 🙂
Nir Sofer did this before either of you. hxxp://nirsoft.net/utils/driverview.html
I’m sorry to disappoint you, but my original driver view utility was present in WARK which is dated like 2002. I simply recycled the code and put it in the Explorer Suite as well.
On top of that, I don’t understand what this has to do with the matter. I wrote in the post:
“Now, the utility is very small and anybody who can write a bit of code can write a similar one in an hour. Still, stealing is not nice. :)”
I understand you quite well. None so deaf as those that won’t hear 😉
I’ve met many people like Martik in the so called scene who make a career out of stealing from others.
I left the pc game cracking scene permanently just because of douches like this guy.
It blows me away how so many of these copy & paste leet script kiddies think they have skillz.
I was struggling with an army of repackers that would not go away and i had to simply stop giving
them all something to repack in the first place..
First off when a repacker steals someone elses work you run the risk of them tampering with things
they know nothing about and could also be infected with malware intentionaly or not..
And if you piss off the crackers they will simply stop posting them. period.
Martik listen up buddy, you need to stop the plagerism and learn to stand on your own two feet.
Besides you never know who you might piss off and i’ve met some seriously dangerous hackers
that can make your life a REAL nightmare. Don’t get me wrong im not trying to threaten anyone
just stating the obvious..
The only crackers that do not mind beeing ripped off in my experience are the ones who steal from others themselves.. sadly its common place acceptable behaviour.
Martik Said
“…I’m not making any money (even 1 penny) from any softwares or keygens. This all just for FUN and as you said hobby!”
~~Does not matter, It’s still illegal in any country and can carry the full weight of that countries legal system. and could result in the repaying of ALL the damages done~~
“Second, why some people crack softwares (commercial ones) and spread them (crack/patch/keygens) over Internet. is it legal or what? do they obey copyright or something?”
~~Does not matter if your breaking laws and international treaties first, second, third or tenth hand …..
“Instead, I rip their keygens and patches and publish them with others name. so whats wrong with that. Cracks has no copyrights, am I right?”
~~Was that an admission? and to answer your question, it’s wrong….and on a side note: If people could get out of legal trouble by PLAYING dumb …. there would be a lot more people out of prison.
_________________________________________________________________________________________
Daniel Pistelli said:
“Second, those who write keygens and cracks are often young boys or generally people who don’t know the damage they cause to developers and small/medium companies.”
~~why are they all boys? and what makes you think they don’t know the damage they can do?…….And yet they are still held accountable (boy, girl, man, woman)
__________________________________________________________________________________________
jsday187 said (I’m posting the whole comment here)
I wouldn’t get to riled up about this supposed “Martik’s” comments. In case some of you are new to the web, there is another hobby people have called “trolling.” What ii is exactly is hard to define with exactness but these “Martik” comments are more than likely a case of it. Sorry to disappoint anyone who thought they were “talking back” so to speak with the “‘REAL’ bad guy.”
~~That was figured out early on ….. Also a lot of people use these websites to get e-mail addies by the drama factor(not saying that this is one of them) however you DOOOOO have to be carefull.
________________________________________________________________________________________
Silk Says::
xpmule really hit the mark (im not posting the comment it was too long of one that in it’s entirety made a point)
it is called “honor amungst theives” in case you were wandering. The legality of the whole thing is beond my scope of experties. however the common sence of it …. a 5 year old would know what was right and wrong in this case.
.
.
.
.
.
Silk Sayd:
“why are they all boys? and what makes you think they don’t know the damage they can do?…….And yet they are still held accountable (boy, girl, man, woman)”
They aren’t all young boys. Many are. I don’t know the scene nowadays. In the past it was mostly young boys. I know that many didn’t realize about the damage because I met quite many and generally speaking a 15-18yo doesn’t really have a clue about what a company earns and how much a crack may damage them.
I don’t think the problem here is a teenager who creates a crack for a program. The problem is other companies or professionals which use this crack to avoid buying a license for the program. I don’t want to ruin the life of a teenager, even if his crack causes a significant loss of sales. I’d rather would like big companies being fined for software piracy. and it’s really incredible how many companies (even big ones) don’t pay for software.
Hi!,
i had the same problem with FUU and this Martik. Check it out: http://crackinglandia.blogspot.com/2010/11/lamerz.html
Just another lammer!.
I originally read this post and then the malware one, thinking they went in that order: some guy steals your software, argues with you about it and then magically, there’s malware floating around with your name on it. After realizing the malware post came first, I couldn’t help but smile.
You know why? What are the chances that this guy, da leet hax0r of da nturnetz, is infected himself from running random programs that he plans to steal? It’s along the lines of all the script kiddies who cheat in multiplayer games, only to have their CD keys stolen from them by the very cheat they’re using. It’d just be really amusing if the software he’s stealing to make money ends up costing him more in the long run by infecting every executable on his machine.
Shitty that innocent peoples’ names are associated, but as close to justice as you’ll probably get without actively pursuing it.
Unfortunately even a moron nowadays is probably cautious enough to run such programs on VMWare or vbox. 🙂
Danny, Martik needs a serious bitch slappin’… why don’t you sue his a$$ just for fun. Then let him know you’ll notify all those other software creators he stolen from and see how much he likes prison. He come out looking like just the hole of a donut. Ignorance may be bliss but jail isn’t! Idiots like this should not be out on the street let alone on the internet.
This quote is classic stupid not to mention a good place to start that suit “Instead, I rip their keygens and patches and publish them with others name. so whats wrong with that. Cracks has no copyrights, am I right?”
Thanks, but I don’t think he’s worth the effort. Being exposed to the public is probably enough of a punishment. 🙂
Daniel…
Enjoyed your approach to the distasteful situation you found yourself in, and learned quite a bit about the darker side of ‘code theft’… I don’t pretend to be a ‘real’ coder, but have spent many an hour trying to make some odd thing work, so I appreciate your frustration in the intellectual rip-off. Kinda goes with ‘man’s inhumanity to man’ …and all that sort of thing these days…
But what stood out to me was your measured response, and unwillingness to be pulled into the slime.
Impressive. I wish more people could respond in a like manner to the little scum bags like Martik. Kudos for you!
Ed Setera
Thanks Ed! 🙂
I like cff explorer